I was recently looking into a PUP that seems to get installed with a freeware called Emotiplus that allows users to use fancy emoticons in Skype.
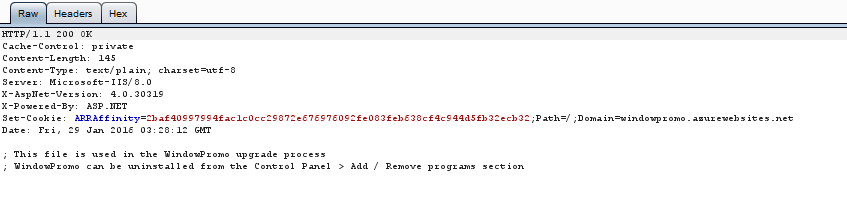
While nothing too bad beyond unwanted requests to dozens of contacts as well as unwanted add-on installation was observed in my test lab, I did see a stream of callbacks to a host: windowpromo.azurewebsites.net

The response looked like the screenshot below:
None of the AntiVirus solutions that I had access to were detecting this particular sample. So I took a stab at creating a ClamAV custom signature for this executable – turned out to be quite simple (though the approach I used is quick and dirty and not the most robust way to identify all variants).
Here is what I did:
Step 1: Run a ClamAV scan on the executable to confirm that the file is not detected as malicious.

Step 2: Run strings on the executable to obtain “signature” string that can be used to create the custom signature for in ClamAV.
Step 3: The results from “strings” was not very helpful, so I decided to use the string “windowpromo.azurewebsites.net” as my signature string. The fact that the installed PUP calls out to this site host makes me reasonably confident that the sample can be detected based on a signature created using this string.
Step 4: I created the hex output for “windowpromo.azurewebsites.net” using the sigtool utility.

Step 5: Created a signature in the following format that ClamAV understands:

The file is saved as “test.ndb”. Two things to note:
- 0 – it is for ClamAv to check for the any file type as target
- “0a” at the end of the hext string has to be removed
This signature us stored in the custom signature database for ClamAV and when running a scan that needs to reference this custom database, the –d switch must be used in Step 6
Step 6: Run clamscan again using the newly created signature
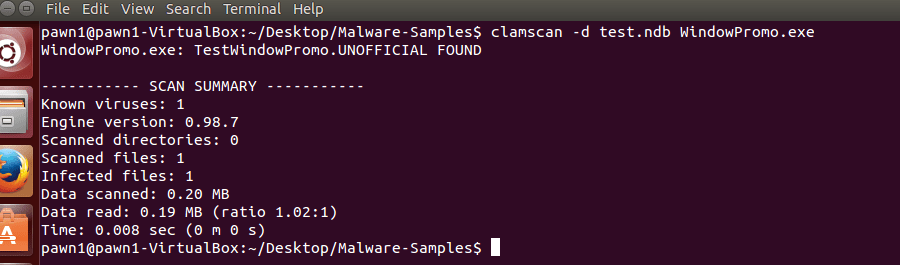
The “.UNOFFICIAL” extension that ClamAV seem to have added is due to the fact that the signature database that we used for this scan is not part of the ClamAV’s project signature database.